Zodiac killer cipher, October 20, 1968, Benicia, California, USA. A motorcyclist found the bodies of a young couple in the alley. A few months later, another couple was shot in a park several kilometers away. The killer later reported to the police station in the telephone booth. In addition to acknowledging his own murder, he also claimed responsibility for the first murder.
zodiac 408 cipher and 340 cipher
On August 1, 1969, the killer sent an e-mail to three local newspapers at the same time, claiming that he was a criminal and proved the details of the killing scene. At the same time, he also put different encrypted text in the e-mail, threatening newspapers must be announced before August 1 (Friday), otherwise, it will be from Friday until Sunday, until killing enough 12 people. In one email, the killer claimed that the ciphertext contained his identity information. These emails have a total of 408 symbols, and they are customarily referred to as 408 ciphers.
The newspaper obeyed his request and disclosed the ciphertext, but unfortunately, although the three ciphertexts were successfully cracked by amateur cryptographers, Donald and Bettye Harden, in a matter of days, they were actually in the ciphertext. Did not provide the identity information of the killer, but declared to the world his purpose of killing: to collect slaves after his death.
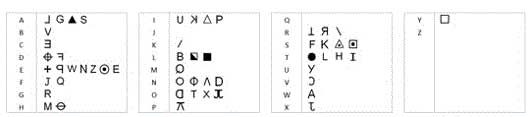
Zodiac 408 cipher text decoding diagram. This ciphertext uses the simplest letter replacement method, but one letter may correspond to multiple symbols. (Figure Zodiologist.com)
What did the zodiac cipher say?
The full text of the decoded content is as follows:
I like to kill people because it is very interesting and more interesting than the game of hunting wild animals in the forest because humans are the most dangerous of all animals. Killing gave me great pleasure, which was more cheerful and thorough than venting sexual desire on a girl. The most important thing is that when I die, I will be born again in heaven, and those victims will become my slaves. I will not reveal my name to you, otherwise you will try to prevent or even prevent me from collecting slaves after death. EBEORIETEMETHHPITI (The meaning of the last symbol is not known yet)
On August 7, 1969, a newspaper office received a letter from the killer. In the letter, the killer first used “Zodiac” (Zodiac) to call himself, and the famous “Twelve House Killer” got its name. From then on, each time he communicates with the newspaper, the start of the zodiac killer must be: “This is the Zodiac speaking.”
Less than a month later, the zodiac killer committed numerous murders and continued to contribute to the newspaper. In addition to continuing to ridicule the police for incompetence, he also said that he was very lonely and nobody paid attention. So he wrote a 340-character ciphertext and asked the newspaper to put it on the headline.
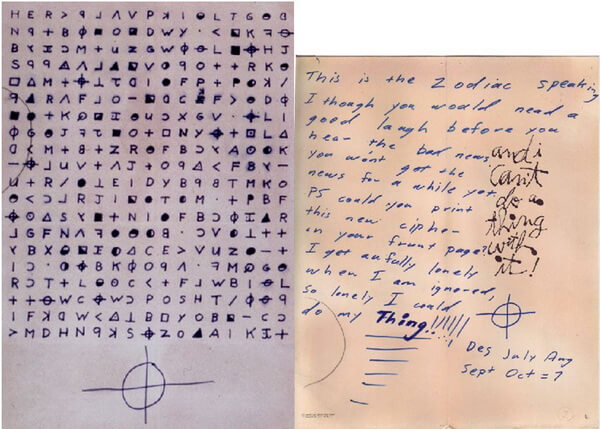
A 340-character ciphertext and a letter sent along with the ciphertext.
Unfortunately, despite the fact that the newspaper has published ciphertext, both the official and the people have tried hard to crack it, but these ciphertexts are always a mystery.
Has anyone solved the zodiac cipher?
Is the password really cracked?
On July 21, 2011, an amateur password enthusiast named Corey Starliper thought he had found the answer and obtained the name of the murderer through password cracking: Leigh Allen ).
His cracked text is this:
KILL/SLF/DR/HELP/ME/KILL/MYSELF/GAS/CHAMBER/AEIOUR/DAY
S/QUESTIONSABLE/EVERYY/WAKING/MOMENT/IM/ALIVE/MY/PR
IDE/LOST/I/CANT/GO/ON/LIVING/IN/THIS/WAY/KILLING/PEOPLE/I/
HAV/KILLD/SO/MANY/PEOPLE/CANT/HELP/MYSELF/IM/SO/AN
GRY/I/COULD/DO/MY/THING/IM/ALONE/IN/THIS/WORLD/MY/W
HOLE/LIFE/FUL/O/LIES/IM/UNABLE/TO/STOP/BY/THE/TIME/YOU
/SOLVE/THIS/I/WILL/HAV/KILLD/ELEVEN/PEOPLE/PLEASE/HELP/
ME/STOP/KILLING/PEOPLE/PLEASE/MY/NAME/IS/LEIGH/ALLEN
Although it was a bit confusing at first, the meaning of the second line was more obvious. The general idea is that he has no dignity, is lonely, and is full of lies in his life, so he can’t help but want to kill. He even said that he hopes that others can help him stop him. Does it feel like a decent model?
However, this so-called decoding has not been recognized by the password community. Corey assumes that the ciphertext encryption method is the famous and easy-to-understand Kaiser password. This kind of password is like shifting two alphabets written from a to z, with the shifted letters corresponding to the original letters. As long as the parties agree on the number of bits to move, they can decode it.
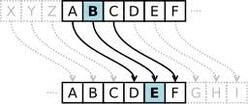
In simple terms, Caesar’s password can be represented by vector addition. Use 0-25 to indicate the 26 letters of az. Then convert the text that needs to be converted (for example, bad) to the row vector a ([1 0 3]) corresponding to the number, and then add the vector according to the number of shifts (such as Caesar-3 is 3 bits backward). A row vector b ([3 3 3]) representing a shift, the resulting vector c ([4 3 6]) is then converted (greater than 25 minus 25) to a letter to get a password (edg).
Why isn’t Cory’s decoding correct? The problem lies in the added row vector b. The principle of Caesar’s password is to perform a fixed shift on the information, so each element of the shift row vector should be the same. For example, in the previous paragraph of Caesar-3, shifting the row vector is [3 3 3]. Of course, in order not to be easy to see, it is also possible to change the values of the elements in the shift row vector, so that although they are regular, they are not so straightforward.
For example, for the word sunrise, the shift vector is a shift of [1 2 3 1 2 3 4]. You can do this: First, get the vector corresponding to sunrise as [18 20 13 17 8 18 4]. Then it is added to the shift vector b[1 2 3 1 2 3] to obtain the cipher vector c [19 22 16 18 10 21 8]. Finally, convert this vector to the corresponding letter to get the password twqskvi. In this example, the displacement of different letters is different, so it is harder to crack it than the simple Caesar’s password with all 3 letters.
For the Zodiac’s 340-character password, Corey thinks it is a variant of Caesar’s password. Since one case of the Zodiac killer was related to the United States Virgin Islands (area code 340), and the total character of the password was 340 words, he thought that 340 should be reflected in the password. After some effort, Corey gets the shift vector b=[3 4 6 3 4 6 …].

Corey’s solution did not follow the rules he set.
However, Corey did not follow the [3 4 6 3 4 6 …] law of displacement. In fact, he did not even follow any law. Take the name of the most critical killer SLEIGHALLEN. Corry first converted the last 11 characters in the password to the English alphabet KSZZOAAIKIT and then converted it to SLEIGHALLEN. However, the shift vector in this transformation is [8 – 7 5 9 -8 7 0 3 1 -4 -6]. This is a hundred thousand miles away from the shift vector he set.
Perhaps Cory’s practice is actually to write a paragraph that he thinks the zodiac killer might say, and then get its corresponding vector c, and subtract the vector a from the original character to get the displacement vector b. . This is why b is completely irregular.
What is even funnier is that in order to make up meaningful words, Corey has to add irrational factors in the process of making up even the conversion of characters to English letters. For example, “q”-like characters are interpreted as p instead of q, and those square characters are decrypted directly without giving the corresponding English letters to obtain e, f, and a.
It is not just a solution to the code. There are other deadly loopholes in Cory’s so-called crack: Although the region code of the US Virgin Islands is indeed 340, this code was only used in 1997.
From the zodiac writing to the newspaper office and the cracked ciphertext, he can feel that he is very fond of killing people and enjoys it. However, the cipher text cracked by Corey said that he was unable to control himself to kill people because of his loneliness, lack of dignity, and his lies in life. The former refers to domineering side leakage when killing, but the latter is ashamed. In contrast, it is not difficult to guess that Cory may be only in his own way thinking in the zodiac killer, thus composing a set of not enough cold text.

Leave a Reply